NightBeacon Platform
Security Operations, Accelerated.
Binary Defense's security operations platform — the engine behind every investigation, every detection, and every response across our MDR service. NightBeacon Command gives you full visibility. NightBeaconAI gives your team an unfair advantage.

Alert volumes are growing exponentially. Breakout times are now under 30 minutes. Attackers operate at machine speed. The traditional MDR answer, more analysts, doesn't keep pace.
NightBeacon was built inside Binary Defense MDR operations to solve this directly. It handles the triage volume no human team can staff for, so you spend time on the decisions that actually require action.
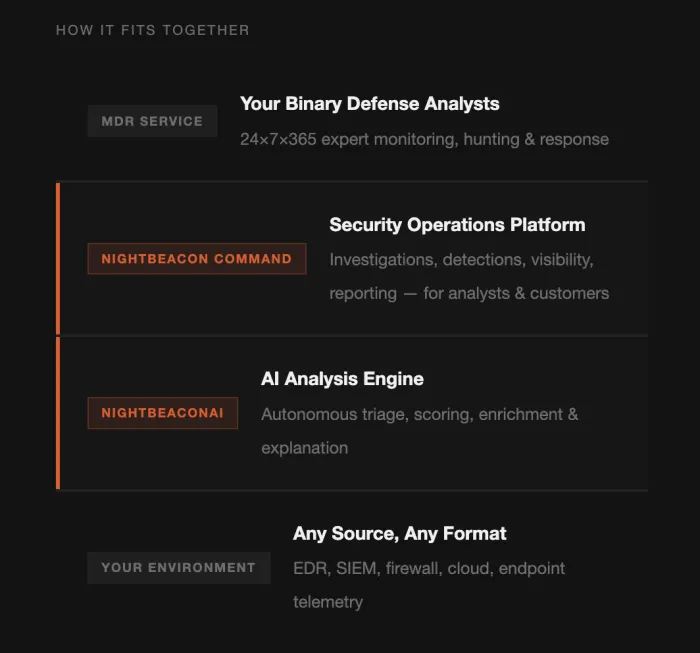
NightBeacon Command is the security operations platform and portal you use to see exactly what we're doing and why. It's what was built to replace the black box of traditional MDR: every investigation, every escalation, fully visible and fully explained.
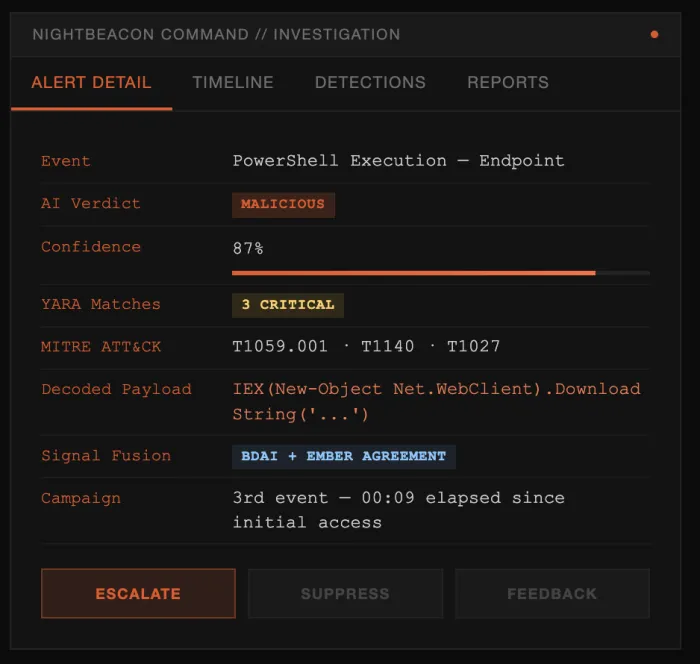
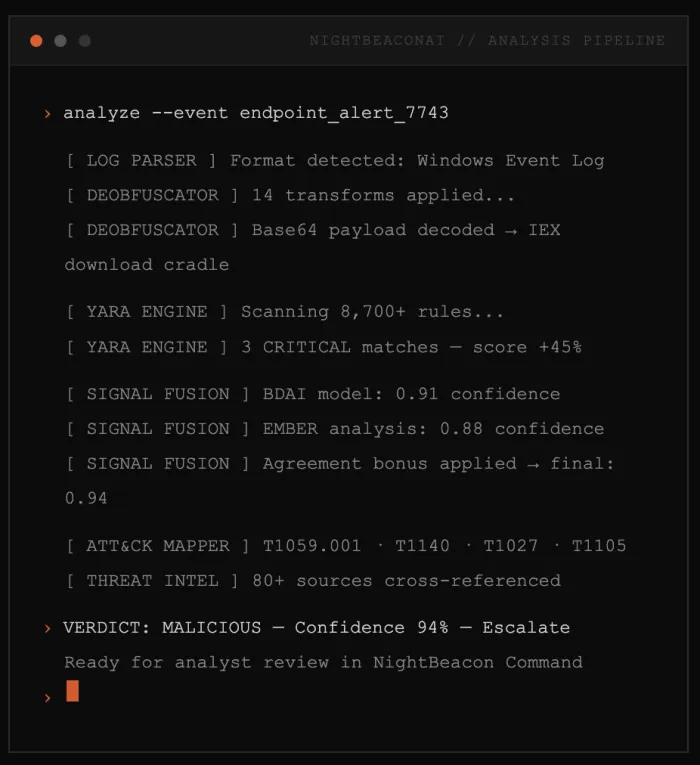
Attackers don't wait for your analyst to finish enriching a ticket. NightBeaconAI processes every event the moment it enters the pipeline — classifying, deobfuscating, correlating across 80+ threat intelligence sources, and mapping to MITRE ATT&CK before a human is ever in the loop.
Your analysts don't investigate. They decide. There's a difference. One takes 20 minutes. The other takes 10 seconds.
NightBeaconAI wasn't designed in a lab. It was engineered inside a live MDR operation by analysts who knew exactly what they needed to catch the threats that slip through everywhere else.
A proprietary ensemble blending Binary Defense's deep learning model with universal log and file analysis, 8,700+ malware detection rules, PowerShell deobfuscation, and phishing analysis. Delivers a single confidence-scored finding with full context before the analyst engages.
Every finding includes plain-language explanations with the specific indicators that drove the analysis, all mapped to MITRE ATT&CK techniques. Analysts present evidence-backed analysis they can defend in front of a board, an auditor, or an incident response team.
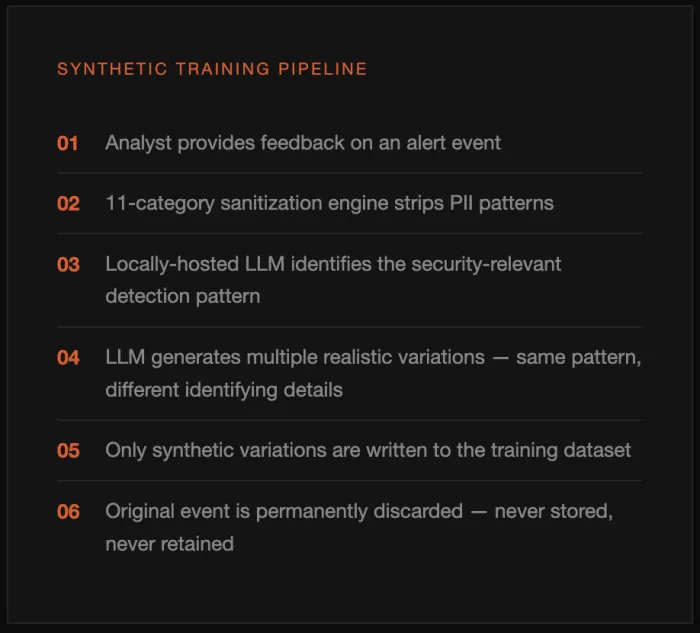
When an analyst makes a call on a finding, that judgment feeds back into NightBeaconAI's learning pipeline — reflecting the accumulated expertise of the entire analyst team. The platform improves continuously from analyst decisions, never from raw customer data.
Detection thresholds calibrate to your environment's unique profile. Suppression rules eliminate known-good noise. Within 60 days, alert quality improves noticeably as NightBeacon adapts to your specific telemetry.
Every AI security vendor has a training data problem. Most solve it by anonymizing customer telemetry. We reject that tradeoff entirely.
NightBeaconAI trains continuously on analyst behavior — without storing, processing, or learning from a single byte of customer data. Not anonymized. Not hashed. Zero.
When an analyst provides feedback, a locally-hosted LLM generates synthetic variations that preserve the security-relevant detection pattern while replacing every identifying detail. Only the synthetic data enters the training pipeline.
The fastest way to understand what NightBeacon does is to watch it in a live MDR context. Request a demo.
Straight answers to what practitioners and CISOs ask most.
No — and that's by design. NightBeacon automates high-volume triage, enrichment, and first-pass classification so analysts focus on the decisions that require judgment. Human analysts retain full authority over every escalation and containment action. The goal is to make each analyst 10x more effective, not eliminate them.
NightBeaconAI uses a six-layer privacy architecture that ensures zero customer data enters the training pipeline. When analysts provide feedback, a locally-hosted LLM generates synthetic variations that preserve detection patterns without any identifying details. The original event is permanently discarded.
Through LIME and SHAP token-level explanations, every classification shows exactly which words, patterns, and indicators drove the model's decision. Contrastive analysis reveals how close the call was. All findings are mapped to specific MITRE ATT&CK techniques so analysts can present evidence, not just a score.
No autonomous containment is permitted without human approval. NightBeacon is designed to reduce the time between alert and analyst decision — not to remove the analyst from that decision. This is a deliberate architectural choice to ensure accountability, especially in regulated environments.
Through a closed-loop continuous learning system. Every analyst thumbs-up or thumbs-down is quality-scored, converted into synthetic training data, and used to retrain the model. Per-customer thresholds auto-tune to each environment's false-positive rate, so the AI reflects the specific threats targeting your customers.
Under 10 minutes. NightBeacon's modular analyzer architecture means new detection patterns added to a specific analyzer module propagate automatically throughout the full pipeline — risk scoring, API, UI, explanation generation. No release trains. No sprints. Research-to-production at the speed threat intelligence is published.
NightBeacon was built inside a live MDR operation — not in a lab. It optimizes for trust, explainability, and sustained decision quality rather than autonomous headcount replacement. Competitors may offer more autonomy; NightBeacon offers more accountability — a meaningful distinction for regulated industries.
No. NightBeacon is the security operations platform that powers Binary Defense MDR. NightBeacon Command and NightBeaconAI are both included when you choose Binary Defense as your MDR provider — already running, already tuned to your environment from day one.
The fastest way to understand NightBeacon is to watch it work. Bring your own log samples or threat files. We'll run them through NightBeaconAI live and show you exactly what you'll get with Binary Defense.