On Wednesday, May 27th, the threat group behind the NetWalker ransomware published initial information about their latest claimed victim, Michigan State University. Binary Defense analysts found a few screenshots of allegedly stolen data that were already published on the site, including what appears to be a financial operating statement from the Physics-Astronomy department from August 2015, and a scanned passport issued by the People’s Republic of China. Other screenshots show lists of files and folders that the attackers apparently had access to. The NetWalker data leak site displays a week-long countdown timer for each set of stolen data. After the timer reaches zero, the stolen data is automatically published unless the victim pays the attackers’ demanded extortion amount. Dan Olsen, deputy spokesperson at MSU, confirmed that the university was recently the victim of a NetWalker ransomware security breach. “Within hours of the intrusion, MSU IT took prompt action and notified law enforcement agencies,” Olsen said. “At this time, we believe the intrusion is isolated to one unit on campus.”
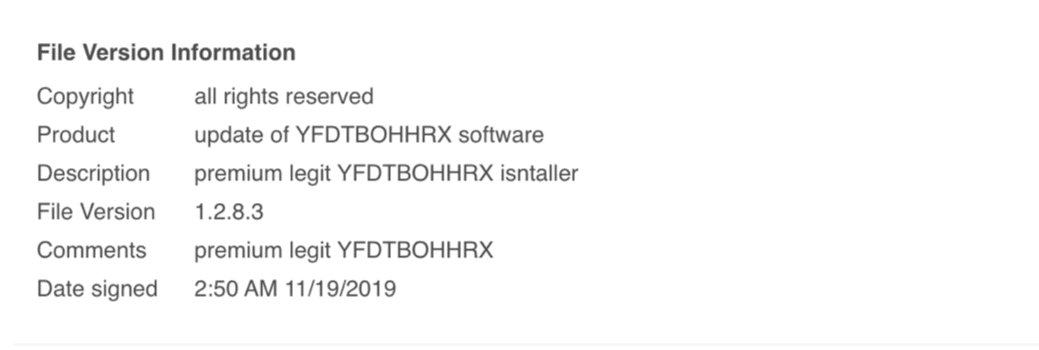
Screenshot from the NetWalker blog on May 29th, 2020.
Analyst Notes
Higher education continues to be targeted by ransomware operators, despite the fact that many state-funded universities are likely facing financial challenges due to increased expenses dealing with campus changes due to COVID-19 and reduced budgetary support from state governments in the near future. Michigan State University’s quick response within hours of the intrusion likely made the difference between an intrusion isolated to one unit on campus and an even more serious breach affecting multiple departments that could have stopped operations and cost more money to recover from. If the university’s IT security staff managed to stop the intrusion before the attackers successfully transferred most of the files they were attempting to steal, it is possible that the data breach will be much smaller and affect fewer staff and students than it might have been otherwise. The key to an effective defense against ransomware and other computer attacks is for a team of skilled security analysts to closely monitor systems 24 hours a day to immediately recognize attacks that slip past other defenses and respond to put a stop to intrusions before major damage is done.
For more information, please read: https://statenews.com/article/2020/05/michigan-state-target-of-ransomware-attack-threatening-to-release-university-data
