Binary Defense Vision EDR can easily detect macro malware leveraging Windows PowerShell and, in this case, helped a customer defend against the Emotet downloader Trojan.
The Binary Defense Vision product has disrupted another enticing phishing email that bypassed a customer’s email gateway defenses and executed malware by an internal user on the endpoint. As much as we don’t like to see successfully phishing attacks we are glad our customer chose Binary Defense Vision to protect their endpoints and ultimately catch this nasty malware execution before any real damage could be achieved. In the case of this specific phishing email, the attack vector was a malicious macro document leveraging Windows PowerShell to download Emotet which is a Downloader Trojan that has been evolving consistently since 2014.
A Phishing Tale
Recipients of this particular attack are sent an email message with a subject line of simply ‘Invoice’ and including body text with the following malicious URL:
- hxxp://blog.digishopbd.com/scan/EN_en/Invoices-Overdue
After a user clicks the link they are immediately prompted to open a malicious macro-malware document called ‘New invoice [RANDOM CHARACTERS].doc’.
In this case, an unsuspecting Director-level employee opened this macro malware document which further executed a Windows PowerShell event and was observed by the Binary Defense Vision Platform 24/7 SOC team.
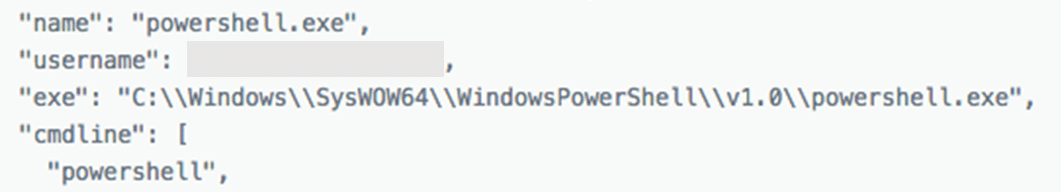
Figure. Binary Defense Vision EDR detects macro malware leveraging Windows PowerShell and attempting to download Trojan Emotet
Binary Defense EDR Catches the Phishing Activity
Our Binary Defense Vision EDR correlated and detected the execution of this PowerShell macro along with the resulting connection to a remote location and promptly alerted our trained SOC analysts to review the suspicious activity. Within minutes from code execution our SOC had analyzed this threat and already escalated communication of the malicious activity to the customer.
The resulting security response from the customer then completely remediated the affected endpoint in under 10 minutes and the incident was closed.
It’s a good thing the Binary Defense Vision SOC team found the Trojan when it did. “Phishing emails can be very convincing,” said SOC Director Todd Kaltenborn, adding that “this Trojan would have been a very effective attack” if it hadn’t been spotted so quickly and estimated “savings of up to $1 million for this customer to remediate this incident”.
Get Vision for Your Security
Binary Defense Vision team is led by visionary David Kennedy and recently introduced Vision 4.0 Platform for Managed Endpoint Detection and Response (EDR) with built-in Endpoint Platform Protection (EPP). This innovative version introduces an array of new endpoint protection features to keep your data, your brand, and your people safe.
Interested in learning more? Check out https://get.binarydefense.vision and join our list of loyal and satisfied customers. And if you’re a current Vision or MSSP customer, don’t be shy about sharing your experience with us—we love to hear your voice as we support your business.