Hackers employ a multitude of methods in order to gain access to a company’s data, but at the end of the day, they are looking for the fastest route to payday. One such method is known as a wire transfer scam. This scam has been around for a while; you’ve surely heard of the famous “Nigerian Prince” that just needs you to send him a little bit of money and will repay you back generously.
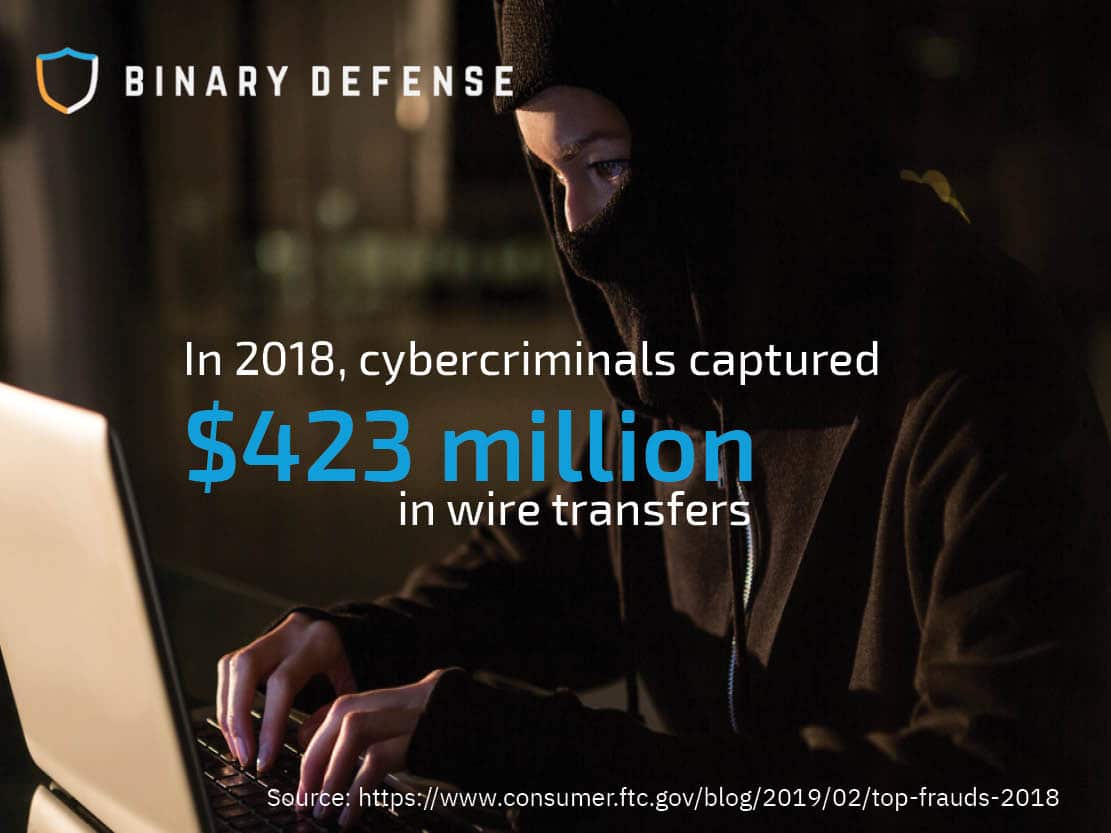
Why wire transfer scams? To be frank, because it works. In 2018, cybercriminals made off with $423 million in wire transfers alone[1].
 Individuals are targeted with a broad range of tactics
Individuals are targeted with a broad range of tactics
Cybercriminals will use a broad range of tactics to gain the wire transfer, including telephone solicitation, false 900 phone numbers, telemarketing scams, unsolicited junk email (aka spam), social media accounts, phony calls from the I.R.S. and other government agencies. The scammers usually threaten some sort of police action or physical harm if you don’t comply.
Although email (including spear phishing) is the most common tactic, other instances can be seen on a smaller scale. Many times, Facebook or Instagram profiles are set up with fake names and locations. These accounts are used to reach out to individuals with claims that they can turn $500 USD into $5,000. All they ask for is account details from the individual and they will return the money via wire transfer. This usually results in the victim’s account being drained of all its funds and the perpetrator gaining access to their account credentials. Similar to mass emails, scammers will also call potential victim’s phones and state that the user has won a prize such as a free vacation or free gas for a year and all they need is personal information such as a name, social security number, and date of birth.
Wire transfer scams can be difficult to spot at work
These days, however, the scams are quite a bit more advanced and harder to detect. In a business scenario, the most damaging scams involve a cybercriminal impersonating a business partner, coworker, client or a company executive or service and request personal account information or for money to be transferred.
On the surface, these solicitations look legitimate. If you’re a subordinate receiving this request from a manager or higher-up in the company, your initial instinct is to do what is being asked of you. Likely you want to make a good impression on your boss and the company leadership for taking action. However, if you’ve never been asked to do a wire transfer before, or the particular request seems odd to you, you should probably put on the brakes and ask yourself (and your manager) some questions.
First, check the sender’s “from” email address. Is it a legitimate email address from your company? If it’s not, that should be your first clue that the sender’s intent isn’t on the up-and-up.
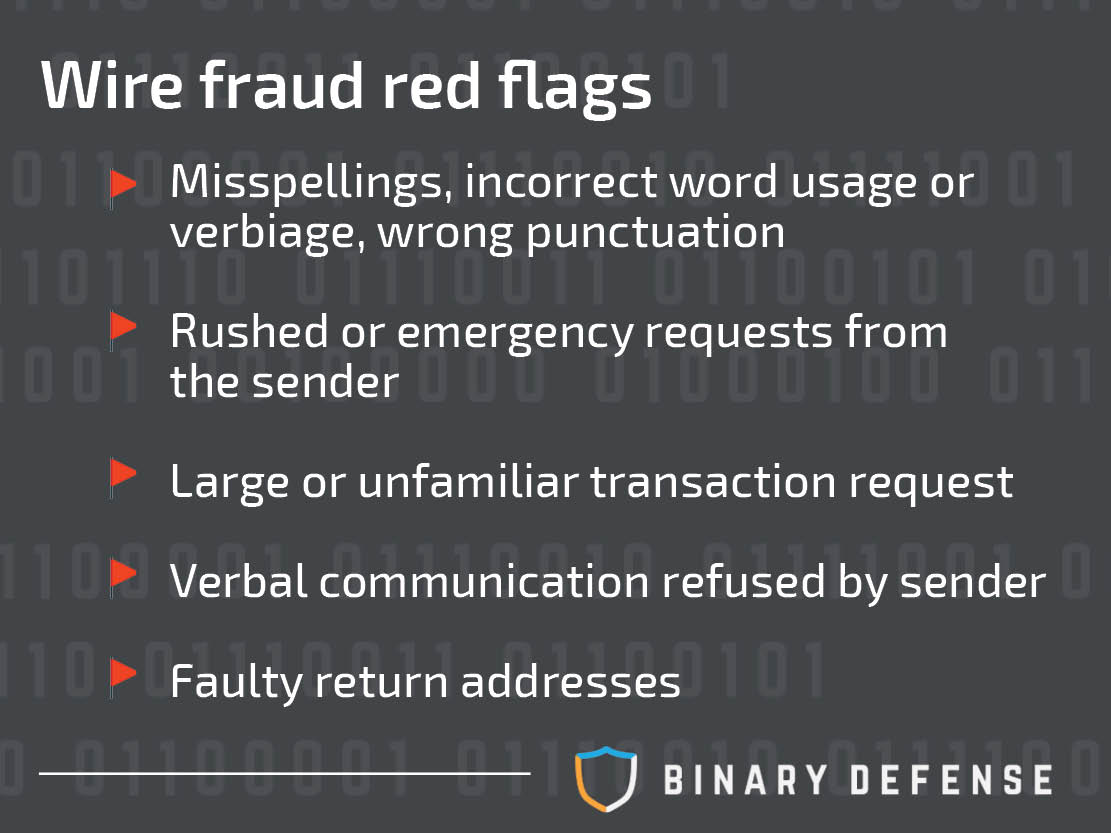
Other red flags that indicate attempted wire fraud via email:
- Misspellings, incorrect word usage or verbiage, or wrong punctuations
- Rushed or emergency requests from the sender
- Large or unfamiliar transaction request
- Verbal communication is refused by the sender
- Faulty return addresses
Create a protocol to avoid wire transfer fraud
How can you avoid having an employee fall into a hacker’s trap? Creating a protocol for wire transfers can help thwart some of the attempts.
Although at times, it can be difficult to detect, wire fraud can be easily spotted if users know what to look for. If your employees are aware of the tactics that are used and red flags that are associated with it, wire transfer fraud is preventable.