With all the news around COVID-19/Coronavirus, the average person is turning to the internet for real-time advice and updates about the pandemic. With the increase in web traffic, cybercriminals are taking advantage of the scare to catch people with their guard down. By creating emails and websites that mirror, and in some cases, function, like legitimate medical sources, cybercriminals are slipping malware onto people’s systems.
According to KrebsonSecurity.com, cybercriminals have duplicated an interactive map of the infections and fatalities from COVID-19 produced by Johns Hopkins University. Fully interactive and functional, the map fools consumers into believing it is legitimate. Users are asked to open an applet, which contains the malware, says Business Insider. This tactic is being used across different malicious websites and spam emails to reach a broad audience. Many of the websites have delivered the AZORult malware, which is designed to steal passwords for online banking, email and other services.
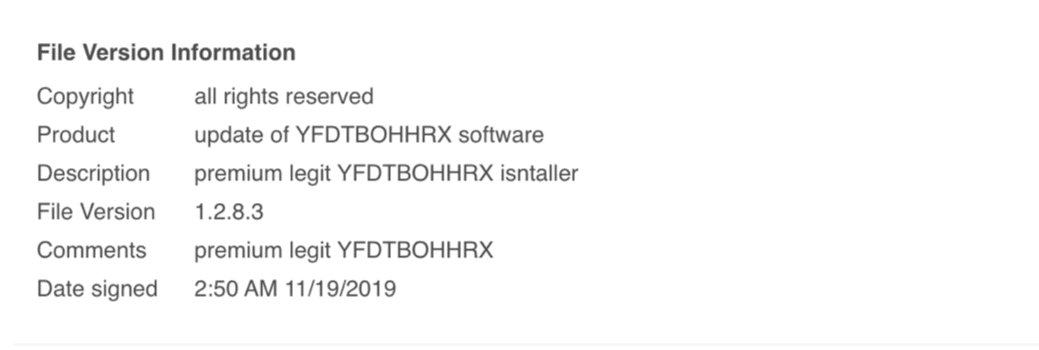
Other efforts include spam emails coming through with genuine health information about the virus but are laced with malware. According to BleepingComputer.com, researchers from MalwareHunterTeam, one such malicious email campaign pretends to be from the Centers for Disease Control (CDC) and includes an attached zip file containing a malware program called MyHealth.exe. If this program is run, it installs the GuLoader malware. Other emails can seem as though they are coming from government sources and contain a Word document purporting to outline best practices, which installs malware when the user opens the document.
The Binary Defense Counterintelligence team is even reporting some activity on dark web where individuals appear to be attempting to sell the virus itself for nefarious purposes—selling vials of COVID-19-infected saliva. These are almost certainly scams meant to take money from people who will not be able to complain to police that they have been defrauded.
How to find the information you need without becoming a victim of a breach
So, how do you still find out all the latest updates on COVID-19 without falling victim to one of these scams? First, only open attachments from trusted sources. It is extremely unlikely that the Centers for Disease Control (CDC) or World Health Organization (WHO) will send direct email messages to individuals who have not subscribed to a mailing list, but attackers often send email pretending to be these organizations. If you receive an email from an organization that you don’t recognize, check the “from” address to see if the sender matches the organization’s domain (e.g. @clevelandclinic.com). Even the “from” address can be spoofed, so don’t rely on that as your only indication that the email is trustworthy.
If an attached Word document or Excel spreadsheet contains instructions to click the “Enable Content” button or urges you to double-click an image inside the document, don’t do it. Enabling content gives permission for potentially malicious code to run and can give an attacker complete control over your computer and its files.
Any important public health information will be available on the official websites of public health organizations and not exclusive to email. If the email is even slightly suspicious, don’t open the attachments or follow links from the email. Instead, use your web browser to visit the website of the agency at an address you know, such as www.cdc.gov.
If an email message contains a zip file, be extra cautious about double-clicking any of the files inside. If the file names end in a file extension you weren’t expecting, such as “.exe” or “.bat”, “.vbs” or “.vbe”, they are programs that are likely dangerous to run.
If a website asks you to download and run a file to install extra functionality or view content, don’t do it unless you are completely sure the website is legitimate, and you know what you’re installing. If in doubt, skip it.